
Let’s be honest, if you’re a student or fresher thinking about your future, cyber security probably sounds exciting. Hacking. Ethical hacking. Big salaries. Working with top tech companies. Maybe even working remotely for international firms.
But then confusion starts. Where do you begin? Do you need coding? Do you need a degree? How long will it take? And most importantly, is cyber security a good career in India?
The short answer: Yes, it is.
The realistic answer: It’s a great career, but only if you’re ready to build strong fundamentals, practice consistently, and avoid shortcuts.
This is not one of those “Become a hacker in 30 days” guides.
This is a complete, practical, 2000+ word roadmap designed especially for students and freshers who want clarity.
Let’s break it down step by step.
Cyber security is not just one job. It’s a field with multiple domains: offensive security, defensive security, cloud security, governance, digital forensics, and more.
Because of this, many students feel overwhelmed. They watch random YouTube tutorials, install tools like Kali Linux, and start running commands without understanding what they’re doing.
That’s the wrong approach. Instead, you need a structured learning path.
Here’s the right roadmap.
Before you even think about hacking, you must understand how computers and networks actually work.
Imagine trying to break into a house without knowing how doors, locks, or windows function. That’s what learning hacking without networking knowledge feels like.
Start with:
Also learn:
Real example:
Many students jump directly to tools like Metasploit. In interviews, when asked, “Explain how DNS works,” they cannot answer. That’s where they fail.
Strong basics = long-term success.
Now let’s talk about degrees.
Most companies prefer:
But here’s the truth.
A degree alone will NOT get you hired.
Recruiters look for practical exposure. Your cyber security qualifications should include:
If you are from a non-technical background, don’t panic.
You can start with:
Many successful security professionals started in IT support before moving into security.
Most freshers don’t realise this.
The majority of entry-level jobs are in defensive security.
Defensive security includes:
Common entry-level roles:
Realistic expectation:
Your first job may involve monitoring logs for hours. It may not feel exciting at first. But this experience teaches you how real attacks happen.
And that experience is extremely valuable.
Now let’s talk about the exciting part, offensive security.
Offensive security means legally testing systems to find vulnerabilities before real hackers do.
Roles include:
But here’s the reality.
Offensive security is NOT beginner-friendly unless your fundamentals are strong.
You must understand:
Real example:
A penetration tester doesn’t just run tools. They:
This requires analytical thinking, not just tool knowledge.
Many professionals work 1–2 years in defensive roles before moving to offensive security.
That’s normal.
Certifications help, especially when you’re a fresher.
Good beginner certifications include:
These cyber security certifications for beginners improve resume visibility.
But remember:
Certification + No Skill = No Job.
Skill + Certification = Strong Profile.
If you feel confused about where to prepare, structured training from a reputed institute can help, provided they focus on practical labs and real-world exposure. For example, academies like Techbyheart Academy emphasize hands-on training, lab environments, and industry-oriented learning rather than only theory. However, even if you join any academy, your personal practice and consistency will decide your success, not just classroom sessions.
The career path of cyber security is flexible. You are not stuck in one role.
You can move into:
Your interest and strengths will decide your path.
If you love analysis and monitoring → Defensive Security.
If you love breaking systems ethically → Offensive Security.
If you enjoy policies and compliance → GRC.
Let’s be realistic.
If you are starting from zero:
If you already have IT knowledge, it may take 4–6 months.
Avoid fake promises like “Become ethical hacker in 30 days.”
Cyber security rewards consistency, not speed.
This is one of the biggest fears among students.
Good news:
Coding is NOT mandatory for all roles.
For SOC roles:
For penetration testing:
For security engineering:
You don’t need to be a software developer. But understanding logic and automation will help you grow faster.
Let’s address real mistakes.
Cyber security is competitive. Smart learning beats fast learning.
India is rapidly digitizing.
This creates strong demand for skilled professionals.
But remember, competition is increasing too.
Only candidates with practical knowledge and strong fundamentals will stand out.
Entry-level salaries may start moderately, but with 3–5 years of experience, growth becomes significant.
Don’t chase hype, Don’t chase tools, Chase understanding.
Starting may feel overwhelming, but following a structured Cyber security career roadmap for students makes everything clearer.
Yes, is cyber security a good career in India? Absolutely, if you approach it realistically.
It is not a shortcut career. It is a skill-based profession that rewards patience, discipline, and continuous learning.
If you stay consistent, build strong fundamentals, and gain real-world experience, you can build a stable, respected, and high-growth career in cyber security.
Your journey may start small. But it can lead to global opportunities.
Is Cyber Security a Good Career in India?As digitalisation increases across industries, the demand for cybersecurity professionals is rising rapidly. From startups to multinational corporations, organizations are investing more in protecting their data and infrastructure from cyber threats.
So, is cyber security a good career in India? The short answer is “yes”, and the long answer is even more promising.
Cyberattacks in India are increasing every year, yet the supply of skilled professionals remains far behind industry demand. This gap creates opportunities for students and working professionals looking for a stable, high-growth career.
Cybersecurity offers:
Whether you have a technical background or are planning a career switch, cybersecurity offers multiple entry points and long-term growth potential.
Let’s explore what makes this field one of the smartest career choices today.
Starting a career in cybersecurity may seem complex, but with the right approach, it becomes highly achievable.
Start by building a strong foundation in:
You don’t need years of experience to enter this field. Many professionals begin with a structured learning process that combines theoretical knowledge with practical labs.
Hands-on experience is essential in cybersecurity because employers value what you can do more than what you know.
Students often wonder which path they should follow to enter cybersecurity. A clear roadmap can make the journey much smoother.
Understand networking, databases, and system administration.
Focus on threat detection, vulnerability assessment, and risk management.
Work on labs, simulations, and real-world scenarios.
Popular domains include:
Certifications validate your skills and improve employability.
Following a structured roadmap reduces confusion and helps you progress with confidence.
To succeed as a cybersecurity analyst, you need both technical expertise and analytical thinking.
Remember, cybersecurity is not just about tools. It involves understanding attacker behaviour and proactively defending systems.
Professionals who continuously upgrade their skills stay ahead in this rapidly growing field.
The cybersecurity job market in India is expanding rapidly, making it an attractive career option.
Salaries vary based on skills, certifications, and experience, but the growth is strong.
India is expected to require over 1 million cybersecurity professionals in the coming years, highlighting the massive talent shortage.
This demand ensures long-term career security.
Certifications play a crucial role in establishing credibility and validating your expertise.
Some widely recognised certifications include:
For beginners, foundational certifications are ideal, while experienced professionals can go for advanced credentials.
However, other than certifications, practical knowledge is what truly sets candidates apart.
Employers steadily prefer professionals who can demonstrate real-world skills.
One of the most common questions aspiring professionals ask is “whether to choose structured training or self-learning?”
While self-learning helps you explore the field, choosing a trusted cyber security institute for guided training can speed up career readiness with a clear path and practical experience.
For many learners, combining structured programs with independent practice delivers the best results.
Returning to the question: is cyber security a good career in India? Without a doubt, it is one of the most promising career paths available today.
With rising cyber threats, growing digital ecosystems, and a major talent shortage, the demand for skilled professionals will only continue to rise.
If you are looking for stability, strong earning potential, and continuous growth, cybersecurity is a strong choice.
Starting your journey with Techbyheart for learning support can help build your skills early to position yourself for success in this high-demand industry.
Cybersecurity Excellence Awards: TechByHeart Recognised by EC-CouncilTechByHeart has been honoured under Cybersecurity Excellence Awards with the EC-Council ATC Circle of Excellence Award 2025. This global recognition stands out as our unbreakable commitment to building future-ready cybersecurity professionals and advancing the digital security ecosystem.
Awarded by the EC-Council (International Council of E-Commerce Consultants), this milestone is reserved for accredited training center that reveal excellence in cybersecurity training, innovation, and workforce development.
The ATC Circle of Excellence Award is EC-Council’s highest recognition, celebrating training partners who consistently offer:
This award places TechByHeart among all groups of institutions shaping the next generation of cyber defenders.
Our approach goes beyond theories; we focus on practical, real-world cybersecurity skills that align with current industry demands, making us a trusted choice for cyber security training and placement.
It’s not just a certification, TechByHeart ensures every learners prepared for real-world challenges
By focusing on hands-on learning, we help fill the gap between academic knowledge and industry expectations.
Winning the ATC Circle of Excellence Award 2025 is a milestone that strengthens TechByHeart’s position as a trusted Cyber Security Institution in India, recognised for its impact on cybersecurity education.
This achievement highlights the dedication of our instructors, the commitment of our students, and the trust placed in us by global accreditation bodies.
Choosing the right training partner matters. With EC-Council recognition and a proven track record, TechByHeart Academy remains the trusted destination for aspiring cybersecurity professionals.

Cyber Security training has evolved, and traditional network security models are no longer enough to combat advanced and modern cyber threats. The growing number of remote workers, cloud services, and mobile devices has expanded the attack surface, making networks more vulnerable. That’s where Zero Trust Architecture comes in, a modern security framework that is fast becoming the future of network security.
Zero Trust Architecture (ZTA) is a security model that operates on the principle of “never trust, always verify.” Unlike the traditional perimeter-based approach, Zero Trust assumes that threats can exist both outside and inside the network. Therefore, no user or device is trusted by default even if they are inside the corporate network.
Zero Trust Architecture verifies every access request as if it originates from an open network. It requires strict identity verification, device compliance checks, and continuous monitoring before granting access to data or resources. Access is granted based on the principle of least privilege, users only get access to what they absolutely need.
Core components of ZTA include:
By eliminating implicit trust, Zero Trust significantly reduces the chances of data breaches caused by insider threats or compromised devices.
As more businesses shift to remote and hybrid work models, Zero Trust offers secure access from any location, improving flexibility without compromising security.
ZTA helps organizations meet regulatory requirements like GDPR, HIPAA, and PCI DSS by enforcing strong access control and data protection measures.
Zero Trust is ideal for cloud environments, offering scalable protection for SaaS applications, cloud storage, and virtual networks.
Zero Trust Architecture is not just a trend, it’s a necessary evolution in the face of modern cyber threats. As organizations strive to protect their digital assets in an increasingly complex landscape, adopting a Zero Trust approach is essential for future-ready network security. By trusting nothing and verifying everything, businesses can build a resilient, secure infrastructure that stands strong against evolving threats.
For further reading on similar topics, check out article on : How to Conduct a Basic Network Scan for Vulnerabilities
Top 5 Cybersecurity Certifications to Boost Your Career
In this era, cybersecurity professionals are in high demand. Whether you’re starting out or advancing your IT security career, the right certification can open doors to top roles and higher salaries. If you’re looking for the Top 5 Cybersecurity Certifications, here’s a list of must-have credentials offered by TechByHeart Academy to strengthen your skills and boost your profile.
The CEH V13 certification is globally recognized and validates your skills in identifying vulnerabilities and preventing cyberattacks. This program at TechByHeart Academy is designed with live practical sessions, hands-on labs, and real-world hacking scenarios, ensuring you learn to think like a hacker and protect systems effectively.
CHFI focuses on digital forensics. This certification teaches you how to investigate cyber crimes, gather digital evidence, and prepare forensic reports that stand up in court. TechByHeart Academy’s CHFI program is ideal for those aiming to work with law enforcement, incident response, or cyber law.
For those looking to step into or advance in Security Operations Center (SOC) roles, the ASA certification is essential. The course dives deep into threat hunting, incident detection, and advanced SIEM management. With TechByHeart Academy’s state-of-the-art labs, you’ll handle complex attack scenarios, preparing you for high-level SOC analyst roles.
The CSA certification is perfect for freshers and IT professionals who want to specialize in monitoring and responding to cybersecurity incidents. TechByHeart Academy’s CSA course includes real-time security event monitoring and incident analysis, providing a strong foundation for SOC operations.
CST is tailored for those aiming to excel in penetration testing and vulnerability assessments. Through TechByHeart Academy, you’ll perform network and application tests in simulated environments, learn to exploit security flaws, and generate professional reports, critical skills for any ethical hacker or security consultant.
All these certifications from TechByHeart Academy come with hands on labs, expert mentorship, and placement assistance. With their practical-oriented approach, you won’t just pass exams, you’ll build the confidence to tackle real-world cybersecurity challenges.
Earning any of these Top 5 Cybersecurity Certifications can set you apart in a competitive market. Whether you dream of becoming an ethical hacker, forensic investigator, or SOC specialist, TechByHeart Academy has the right course to kickstart or elevate your cybersecurity career.
Ready to secure your future? Enroll now and start your journey toward becoming a sought-after cybersecurity professional!
Is Public Wi-Fi Safe? Here’s What You Should Know

In today’s hyper-connected world, public Wi-Fi is everywhere in coffee shops, airports, hotels, and malls. It’s incredibly convenient, especially when you’re on the go and need quick internet access. But while public Wi-Fi might be free, it could come with hidden costs like the risk of your personal data being exposed to cybercriminals, a common concern raised in cyber security training programs
So, is public Wi-Fi safe? Let’s break it down.
One of the most common threats on public networks is a Man-in-the-Middle (MitM) attack. This occurs when a hacker intercepts the communication between your device and the website or service you’re using. They have the ability to steal financial information, login credentials, and other private information.
Certain public Wi-Fi networks do not use encryption, so the information you send and receive is not secure. Your online activities could be intercepted by anyone on the same network.
Cybercriminals often set up rogue Wi-Fi networks that mimic legitimate ones. If you connect to one of these “evil twin” hotspots, the hacker can monitor everything you do online including logging into email or bank accounts.
Some attackers exploit vulnerabilities in public Wi-Fi networks to inject malware into your device. Once infected, they can monitor your activity, steal data, or lock you out of your own files through ransomware.
Using public Wi-Fi doesn’t have to be risky if you take the right precautions. Here are some smart steps you can take to protect yourself:
A VPN encrypts your internet traffic, making it nearly impossible for hackers to intercept or read your data. It’s the most effective tool for securing your connection on public networks.
Try not to log in to banking sites or enter personal information while on public Wi-Fi. Save those tasks for a secure, private network.
When connected to public Wi-Fi, disable file sharing, Bluetooth, and Airdrop (on iOS) to prevent unauthorized access.
Always check that the websites you visit use HTTPS not just HTTP. The “S” stands for secure and indicates encrypted communication between your web browser and the website.
Outdated apps and operating systems may have vulnerabilities that hackers can exploit. Regular updates help keep your device protected; it’s the best practice highlighted at Techbyheart.
Although public Wi-Fi is very helpful, it’s not always secure. In a world that prioritizes digitalization, it is crucial to recognise the risks and take preventative measures to safeguard your data. This awareness is important for students pursuing a career in BCA in Cyber Security, where they learn how real-world cyber threat works. Make sure you connect safely and use your browser sensibly, whether you’re checking your emails in a coffee shop or making a travel reservation at the airport.
Remember: If it’s free, you might be the product.
For further reading on similar topics, check out article on : How to Protect Your Smartphone from Cybersecurity Threats: A Complete Guide
Troubleshooting Common Installation Errors in Kali Linux on Virtual Machines(A beginner-friendly troubleshooting guide to save you from installation headaches!)
Installing Kali Linux in a virtual machine (VM) like VirtualBox or VMware is a great way to dive into cybersecurity without messing up your main system, if you follow the proper guidelines on how to install Kali Linux in VirtualBox. But let’s be real, sometimes things go wrong, and error messages can feel like they’re written in alien code. If you’ve ever stared at a frozen installer or a cryptic error, don’t panic! I’ve been there t
oo, and in this guide, I’ll walk you through the most common Kali Linux VM installation fails and how to fix them.
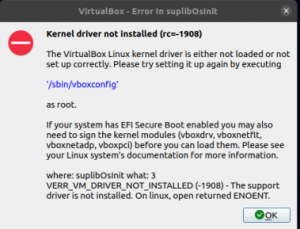
What’s happening?
* Failed to install linux-image-amd64
* The kernel could not be installed
Why?
How to Fix It:
(Pro Tip: If it keeps failing, try a different Kali ISO version—sometimes the latest one has quirks.)
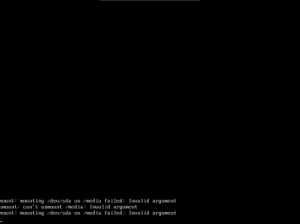
Error Message:
mount: mounting /dev/sda on /media failed: Invalid argument
Why?
How to Fix It:
(If you’re not sure, stick with the automatic installer—it’s way easier!)
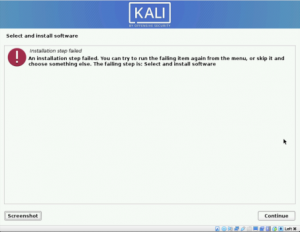
The Problem:
How to Fix It:
✔ In manual partitioning:
✔ If GRUB fails:
(Still stuck? Try reinstalling with “Guided Partitioning” instead of manual.)
What’s happening?
Why?
How to Fix It:
– sudo apt update && sudo apt install kali-linux-default
🔄 Try a different Kali ISO if it keeps failing.
(Fun fact: You can install Kali with just a command line first, then add a GUI later!)
Many of the installations happen due to a lack of fundamentals, that’s why cyber security training with hands-on lab exposure helps learners avoid common mistakes whenworking with Kali Linux
Error Message:
No space left on device
Why?
How to Fix It:
Resize the VM disk (if using VirtualBox):
VBoxManage modifyhd kali.vdi –resize 30000 # Expands to 30GB
Or, just recreate the VM with a bigger disk (easier for beginners).
(Pro Tip: Use dynamically allocated storage so the disk grows as needed.)
🔹 Use the latest Kali ISO (get it from kali.org).
🔹 Enable virtualization (VT-x/AMD-V) in your BIOS for better performance.
🔹 Allocate enough resources:
🔹 Check logs if stuck ( Ctrl + Alt + F4 switches to terminal view).
Kali Linux is an amazing tool, but VM installations can be tricky. If you hit a wall, don’t give up! Most errors are fixable with the right tweaks. Which error did you run into? Let me know in the comments—I’ll help troubleshoot! (And if this guide saved you hours of frustration, share it with another aspiring hacker!)
For further reading on similar topics, check out article on : How to Configure Network Adapters in VirtualBox: A Complete Guide
Top Beginner-Friendly CTF Platforms and Challenges to Start Your Cybersecurity Journey
Ever wanted to “hack” like in the movies—but legally and ethically? Capture The Flag (CTF) challenges are your gateway into the exciting world of cybersecurity. Whether you’re a total newbie or just dipping your toes into hacking, CTFs offer a fun, hands-on way to learn real skills.
In this guide, I’ll break down:
✔ What CTFs are (and why they’re awesome for beginners)
✔ The best beginner-friendly platforms to start with
✔ Easy challenges to try today
✔ Pro tips to avoid frustration & level up faster
Let’s dive in!
Imagine a game where you solve puzzles, crack codes, and find hidden “flags”—but instead of treasure, you’re uncovering cybersecurity secrets! CTFs simulate real-world hacking scenarios in a safe, legal environment, making them perfect for learning.
1. Jeopardy-Style (Best for beginners!)
– challenges in categories like Web Hacking, Cryptography, Forensics.
– You solve tasks to find hidden flags (e.g., FLAG{Th1s_1s_4_Fl4g}).
2. Attack-Defense (Advanced)
– Teams hack each other’s systems while defending their own.
👉 If you’re new, stick with Jeopardy-style CTFs—they’re like mini cybersecurity escape rooms!
– Ever read about SQL injection but had no clue how to actually exploit it?
– CTFs force you to apply theory in real challenges.
– No risk of breaking laws (unlike randomly testing websites).
– All challenges are designed to be hacked.
– CTFs teach you to think like an attacker, spotting weaknesses before bad
guys do.
– Employers love CTF experience—it proves you can solve real problems.
(Fun fact: Many pro hackers started with CTFs!)
Why?
– Walkthroughs & guided learning paths (like “Complete Beginner”).
– No setup needed—hack directly in your browser!
– Free tier available (paid unlocks more content).
Start Here:
– Room: “Intro to Cybersecurity”
– Room: “OverTheWire Bandit” (Linux basics)

Why?
– Beginner-friendly machines with step-by-step tutorials.
– Gradually increases difficulty.
– Free tier + VIP for extra challenges.
Try This:
– “Tier 0 Machines” (Easy boxes with guided help)

Why?
– Teaches Linux commands through a fun, game-like format.
– No installations—just SSH into their server!
– 100% free.
First Challenge:
– Level 0 → 1: Basic SSH login & file navigation.
(Pro tip: If you don’t know Linux yet, start here!)

Why?
– Designed for high schoolers (but great for all beginners).
– Simple, fun challenges with hints & solutions.
– Free & annual competition (with prizes!).
Try:
– “General Skills” challenges (basic commands, encoding).
| Platform | Challenge | What You’ll Learn |
| TryHackMe | “Google Dorking” | How hackers use Google to find secrets |
| HTB | “Meow” (Tier 0) | Basic network scanning & login bypass |
| OverTheWire | Bandit Level 1-5 | Linux commands ( ls , cat , ssh ) |
| PicoCTF | “Obedient Cat” | Reading files & finding flags |
(Just copy-paste the platform name into Google to find them!)
(Don’t worry—you’ll learn these as you go!)
CTFs might seem hard at first, but every expert was once a beginner. The key? Consistency. Solve one challenge a day, and in a few months, you’ll be shocked at how much you’ve learned.
“The only way to learn hacking is to hack (ethically)!”
Which platform will you try first? Let me know in the comments! 👇
(Share this guide if it helped you—more hackers = safer internet!)
Understanding Malware and Its Detection
Let me tell you a story about my friend Sarah. Last month, she clicked on what looked like a harmless PDF attachment in an email. Within hours, her computer slowed to a crawl, strange pop-ups appeared, and worst of all – all her family photos were locked behind a ransom demand. That’s malware in action, and it’s scarier than any horror movie because it’s real.
In this guide, I’ll walk you through the dark world of malicious software using plain language and real examples. No tech jargon, just straight talk about how these digital threats work and – more importantly – how you can protect yourself. Thinking about learning cybersecurity in a structured, practical way, Techbyheart Academy is your next step.
Imagine malware as a gang of digital criminals, each with their own speciality:
Remember the “ILOVEYOU” outbreak in 2000? That was a virus that spread through email attachments disguised as love letters. Like a biological virus, it needed someone to open the attachment to spread. Today, viruses still hide in:
Worms are the ninjas of malware. The infamous WannaCry attack in 2017 didn’t need anyone to open a file – it slithered through network connections on its own, encrypting files in hospitals, businesses, and government systems worldwide.
That “free” game crack or “urgent Flash Player update” you downloaded? Could be a Trojan. I once helped a small business owner who installed what he thought was accounting software, only to find his bank accounts emptied days later.
Picture this: You arrive at work and every file has been renamed to “PAY_OR_LOSE_YOUR_DATA.” That’s ransomware. The city of Baltimore was paralyzed for weeks by a ransomware attack that cost over $18 million to recover from.
Some malware doesn’t break things – it watches you. There are cases where spyware has:
Your computer has ways of telling you something’s wrong – you just need to listen:
The “This Doesn’t Feel Right” Signs:
When It’s Really Bad:

After helping dozens of people recover from infections, here’s what actually works:
Free tools like Malwarebytes (for scanning) combined with Windows Defender (always-on protection) catch most threats. For businesses, I recommend paid solutions like Bitdefender GravityZone.
That “update available” notification you keep ignoring? That’s like leaving your front door unlocked. The WannaCry worm only worked because people hadn’t installed a Windows update that patched the vulnerability.
Keep:
Ask yourself:
Cybercriminals are getting craftier:
1. –Tonight: Run a full malware scan and check for pending updates
2. – This Week: Set up automatic backups if you haven’t already
3. – This Month: Have a family meeting about online safety (yes, really)
Remember Sarah from the beginning? After her ordeal, we set up proper backups and security. When another attack came six months later, she simply wiped her computer and restored everything – no panic, no ransom paid. That’s the power of being prepared. Stay safe out there!
For further reading on similar topics, check out the article on: What Is Social Engineering? | The Psychology of Social Engineering
Is a Cybersecurity Course Really Worth It in 2026?
In 2026, cybersecurity is no longer optional; it’s essential. As cyber threats become more advanced and frequent, the demand for qualified professionals is exploding. This brings us to a key question many students and working professionals are asking: Is a Cybersecurity Course Really Worth It in 2026?
With companies relying heavily on digital infrastructure, the risks of data breaches, ransomware, and cyberattacks are at an all-time high. From small startups to global corporations, organizations are investing millions in cybersecurity systems and, more importantly, in cybersecurity talent.
Cybersecurity roles are no longer limited to tech companies. Healthcare, finance, education, retail, and even government sectors now require specialists to protect sensitive data. This shift has created a global talent gap, with millions of job openings projected by the end of 2026.
Today’s cybersecurity courses are designed to equip learners with both foundational knowledge and hands-on experience. A good course should include:
– Real-time simulation labs
– Practical ethical hacking sessions
– Industry-recognized certifications
– Access to expert mentors
– Placement assistance
One institution leading this movement in India is TechByHeart Academy.

TechByHeart Academy is one of Kerala’s fastest-growing EC Council-accredited cybersecurity training institutes, offering in-depth, career-focused courses tailored to meet industry demands. The TechByHeart provides:
– Certified Ethical Hacking (CEH) and other globally accepted certifications
– Hands-on labs and real-world projects to build practical skills
– Expert trainers with industry experience
– Placement support and career guidance for students
– A strong presence in Kochi, Kottakkal, Trivandrum, Bengaluru, Chennai, UAE & UK, helping local talents tap into global job markets
Whether you’re a student fresh out of school or a working professional looking to switch careers, TechByHeart Academy offers flexible programs that make cybersecurity education accessible and impactful.
Cybersecurity specialists are among the highest-paid IT professionals in 2026. Job roles such as Security Analyst, Penetration Tester, Cybersecurity Consultant, and SOC Analyst are in high demand. With the right training from institutes like TechByHeart Academy, students can confidently pursue careers not only in India but also in international markets like the UAE, the US, and Europe.
So, is a cybersecurity course really worth it in 2026? If you’re looking to future-proof your career, gain high-income potential, and make a real-world impact, the answer is definitely yes. And with trusted academies like TechByHeart Academy, you can start that journey with the right foundation and support.